
There’s nothing like a great vacation with friends or family: warm weather, hiking trails, or even a staycation to go try all the new restaurants and activities where you live. While a vacation means time away from work to recharge and relax, it’s also time away from managing your email inbox. It’s safe to say that everyone, to some extent, dreads that first day back to work where they’ll have to go through hundreds of new emails to find the important ones and catch up on what progressed over their time off. But what if it didn’t have to be this way?

Wide Format printing is an essential part of many organizations. Things such as maps, banners, blueprints, and more are a core part of these organizations, and factors such as quality and production time play a major role in their operations. KIP Wide Format devices address all these areas and more, making their products ones you don’t want to miss.

If someone were to ask you how much your organization spends on printing every year, would you know the answer? Would you know whether your employees are having a positive or negative experience with printing? Although some of you may know these answers, there are a lot of organizations that don’t ask these questions and as a result lose productivity and pay more than necessary. A print assessment is the first step in resolving these issues, which makes it an important step for organizations of any size to take.

Cyber Security is an ever-changing landscape that requires constant monitoring and adaptation. Hackers and malicious users are always looking for new ways to gain access to your sensitive information, and some of these newer methods may be ways you’ve never considered before. Here are 8 cyber security tips to keep you and your business safe this holiday season.

With the holiday season kicking off, many people are going to be turning online to do their shopping. Black Friday and Cyber Monday deals are great places to save, however, they’re also perfect opportunities for hackers to attempt to steal your information and scam you. Here are some tips on how to stay safe while shopping online.

Chromebooks have been a prominent part of many schools due to their ease of use and cost-friendliness, however, there's been a shift to Microsoft Windows devices over Chromebooks in schools lately. What's causing this shift, and why are schools choosing Windows devices over Chromebooks?

Back in 2021, PaperCut released a new powerful print management solution: PaperCut Hive. Designed for SMBs that couldn’t manage printing because of high costs, PaperCut Hive is the perfect SaaS solution to combat those issues. But what is PaperCut Hive, and how does it work?

With AI and machine learning at the forefront of new technologies, it was only a matter of time before it was implemented into the cybersecurity world. With traditional antivirus software falling short and an increasing need for faster reactions to malware a new solution was created – Endpoint Detection Response, or EDR. But what is EDR, and how does it work?

Smishing is the latest tactic cybercriminals have taken on to trick people into giving away their confidential information.

The shift to work-from-home (WFH) and hybrid work models are starting to look like more permanent options for many organizations. This transition is requiring many businesses to make long-term decisions on how to equip home workers with the tools and hardware needed to do their jobs.
Reimagine productivity with Microsoft 365 and Microsoft Teams. Microsoft 365 with Microsoft Teams can help your business improve cybersecurity, reduce costs, and empower employees to work from anywhere. Here we will outline the different offerings between each Microsoft 365 Business Plan to help determine which is the right fit for your organization.

When choosing an Office Suite for your business, the top choices in the marketplace today are Microsoft Office 365 and Google G Suite. Each one offers professional business email and productivity tools for easy collaboration. Both are subscription-based, charging businesses per-person fees every month, with varying levels of subscriptions, depending on the capabilities you are looking for.

After COVID, the world of work will never be the same. The pandemic changed how people feel and think about where and how they work. We’re sharing some key insights into these shifts and the ways we can help your workplace evolve for your new normal.

Whether it’s a question about a product or service, a new order, a support issue, or simply trying to pay a bill, customers still need a human connection when they’re looking for help—and the right cloud communications platform – that includes calling, video conferencing, chat, and secure file sharing provides just that.

Office equipment including desktop computers, collaboration displays, and printers are an investment towards the future and success of your business. While you may be tempted to save money by using your aging equipment until the day it breaks down, this strategy can wind up costing you more in the long run through a loss of productivity and unnecessary expenses.

Safety is a concern for every organization. These days, it’s the safety of their employees and visitors that is the primary focus. Did you know that with PaperCut, you can release jobs from your mobile phone without having to touch the MFP at all?

Studies have shown that uncomfortable environmental conditions can negatively affect performance in the office and meeting rooms, and this is no different in our home workspaces. Few factors are more important to maintain concentration than access to fresh air, natural light and a comfortable temperature.

Small businesses like yours are important. They create jobs, support a competitive marketplace, and lift up local communities. As a small business owner, you’ve worked hard to start your business and make it into something you can be proud of. That’s why it’s important to know how to protect your employees and customers from a range of cyber and financial threats.

The Worldwide Pandemic has created top of mind awareness for every person in the world and has also created awareness in the reopening of corporate America in a post pandemic world. The touchless voice control solution for Xerox Office Equipment minimizes physical contact without slowing you down.

Covid-19 has changed the way we do a lot of things. From frequent hand washing, to constantly cleaning high-touch surfaces, we are all finding ways to adapt to this new normal. Technology has shifted to find new ways in which we can do everyday things with less contact than we did just a couple of months ago.

Here are top tips for employers to ease your employees back to the workplace Post-COVID-19 and give them confidence in their work environment. It is important to be open and transparent with workers on the return-to-work process.

As technology continues to evolve, cyber threats continue to grow in sophistication and complexity. Cyber threats affect businesses of all sizes and require the attention and involvement of chief executive officers (CEOs) and other senior leaders. To help companies understand their risks and prepare for cyber threats, CEOs should discuss key cybersecurity risk management topics with their leadership and implement cybersecurity best practices.

In the wake of challenging times around COVID-19, we are here to help. Providing you a Work from Home solution that is functional, comfortable and made to last. So you can focus on the moments that matter most right now. Here are some tips to creating a space that is comfortable, functional and minimizes distractions.

In response to circumstances resulting from COVID-19 (Coronavirus disease) many workplaces now need to quickly implement new processes for remote work. While your physical locations will change during this difficult time, as a company you want to stay connected and maintain business operations by providing technology that enables your employees to work from anywhere.

Learn the best procedures to disinfect your workplace and home, along with the best steps to protect yourself from COVID-19 based on CDC recommendations.
The Cybersecurity and Infrastructure Security Agency (CISA) warns individuals to remain vigilant for scams related to Coronavirus Disease 2019 (COVID-19). Cyber actors may send emails with malicious attachments or links to fraudulent websites to trick victims into revealing sensitive information or donating to fraudulent charities or causes.

Keeping your internet-connected devices free from malware and infections makes the internet safer for you and more secure for everyone. Protect your devices from malware to keep a clean machine.
The NEW, FREE, Google Cloud Print alternative & Bring Your Own Device (BYOD) solution: Papercut Mobility Print. Whether you’re a current PaperCut user or not, Mobility Print is a free solution aimed at making easy BYOD printing a reality for everyone.

Of all the factors to take into account when buying a printer for your small or medium business, the price tag is just one. And its importance fades quickly when you consider total cost of ownership (TCO) factors such as life expectancy, toner costs and downtime.

If you’re responsible for your company’s IT, you might be surprised by the impact document-based processes have on your day-to-day operations. On average, printing and document management represent 15% of an SMB’s overall IT budget and accounts for at least 12% of IT resources.

Employees are a crucial resource at any business. There are steps you can take now, and during the flu season, to help protect the health of your employees. Create a plan and have your office stocked up with the right supplies.

Data security used to be a concern relegated to large enterprises. Small and medium size business (SMB) owners were more likely to worry about their information security as customers than in a business context. But as the digital age evolves, the security threat landscape is becoming more complex, and SMBs are increasingly in the crosshairs.

Do you know the benefits of a well-stocked breakroom? Creating a space for employees to relax and recharge improves happiness, health, focus, productivity and mental performance. A short break can also decrease stress, on-the-job accidents, soreness, musculoskeletal disorders, and eye strain.

If technology gives your organization a competitive edge, you are familiar with how expensive it is to keep it current. Now, consider that at times, the purchase price of your technology is only a fraction of the cost of the total cost of ownership.

Quickly and accurately retrieve, manage, and share your business documents to increase efficiency and eliminate data entry errors! GlobalSearch® document management software is a cost-effective solution for improving the storage, organization, and monitoring of documents relating to your everyday business processes.

The mobile genie isn’t going back in the bottle, and that’s okay. Being mobile is good for business. It’s part of digital transformation, and it helps us respond faster. Learn how a mobile document workflow strategy can improve your overall service and employee satisfaction.

It can happen to the best of us—your shiny new phone, tablet or laptop, left in an airplane seat pocket or stolen at the local coffee shop when you got up for a refill. Imagine losing the device that connects you to the outside world, and most importantly, your work.
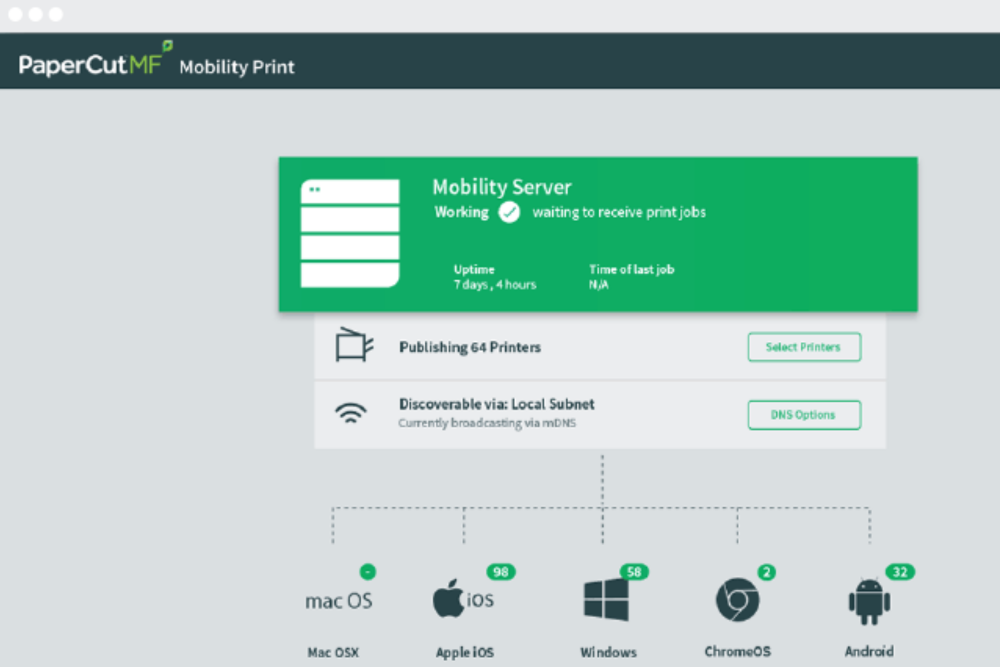
If you’re looking to offer managed support for the widest range of mobile devices connecting to your network, then it’s time to develop your mobile strategy. Planning for, and facilitating mobile print solutions using your existing print infrastructure is made easier with PaperCut’s Mobile and “Bring Your Own Device” (BYOD) features.

At the end of 2015, more than 100 Billion Mobile Apps had been downloaded from the Apple App Store. Social media apps have spread like wild fire among mobile users. Since apps have become more available and accessible people are able to do more with their mobile devices. This mobile trend has lead to the development of mobile apps for business.

The future of work is mobile. But you may be worried that working from anywhere, on any device, could expose you to added security risks. Whether you’re a road warrior or remote worker here are some simple tips to stay protected.